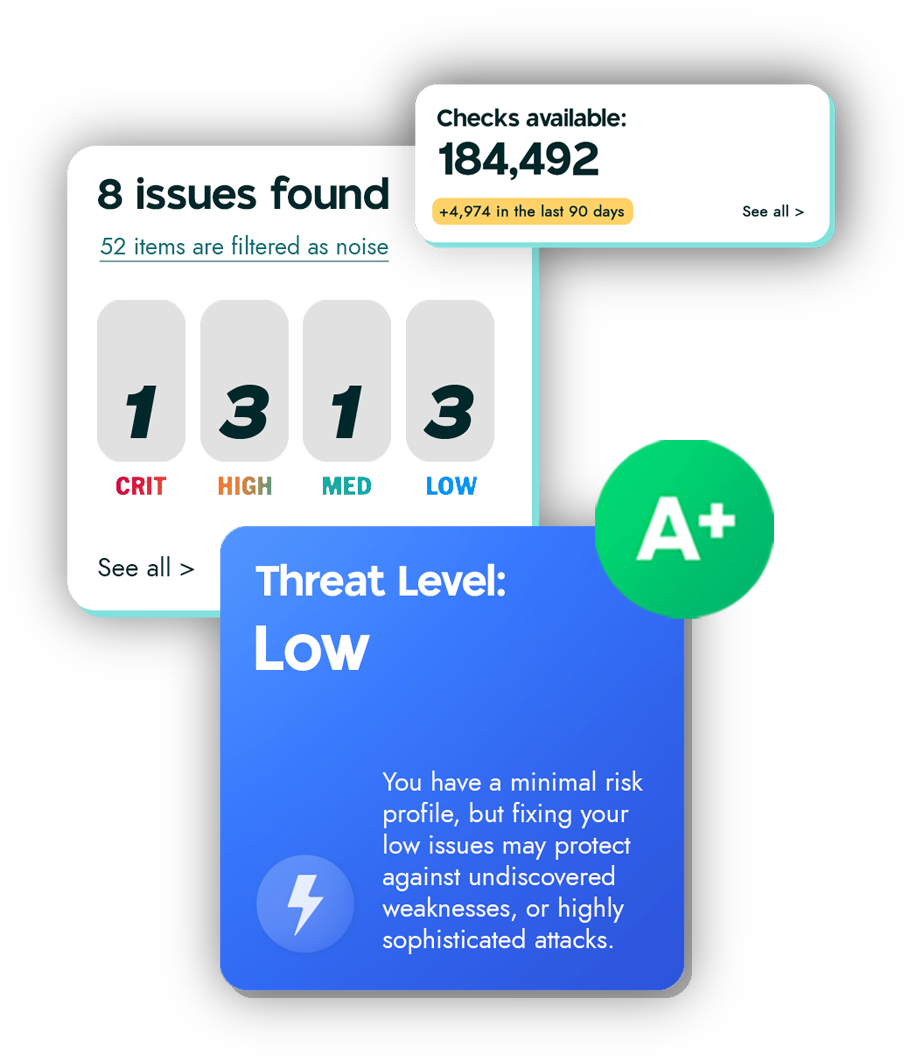
External Scanning Attack Surface Monitoring DAST Website Security Risk Based Prioritization API Security Integrations Emerging Threat Detection CSPM Compliance Cyber Hygiene Reporting Internal Scanning
Compare Vullify
Qualys Alternative Tenable Alternative Rapid7 Alternative Intruder Alternative Detectify Alternative Acunetix Alternative Invicti Alternative Pentest-Tools AlternativeSecurity
Blog Cyber Glossary Vulnerability DatabaseCustomers
Help Center Customer Stories Developer Hub